Issues with Mounting a CIFS Share on the vRO Appliance
This article on the vCOTeam site details how to mount a CIFS share on the vRO Appliance so that workflows can write files directly to a Windows File Share rather than using another process to copy the file over there.
This was straightforward to implement in a lab scenario, however within a corporate environment with more restrictions around security and networking it can potentially be more of a challenge. Specifically we encountered the following error response from a Windows Server seemingly configured correctly for Share and NTFS permssions on the folder to mount:
Status code returned 0xc0000022 NT_STATUS_ACCESS_DENIED CIFS VFS: Send error in SessSetup = -13 CIFS VFS: cifs_mount failed w/return code = -13
This post on a Centos forum helped us track down the problem, i.e. there was at least one Group Policy restricting the use of NTLM.
“It turned out in my case to be a Group policy which was set to Send NTLMv2 responses only. Refuse LM and NTLM. I changed this to Send LM & NTLM -use NTLMv2 session security if negotiated.
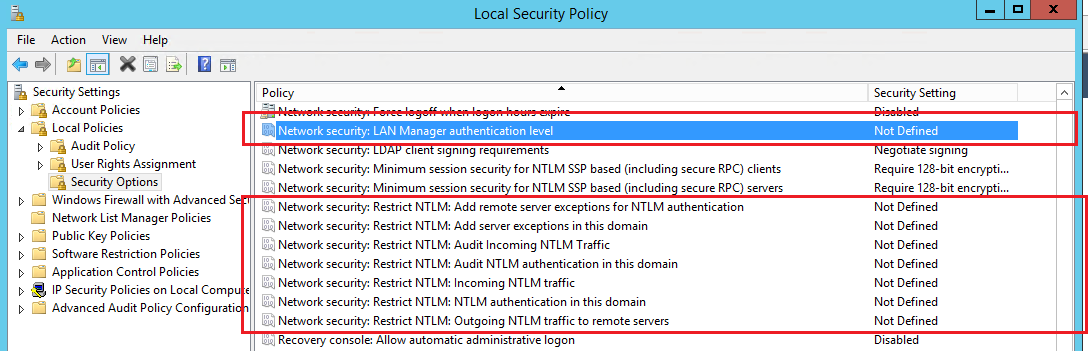
Located at: Computer Configuration/Windows Settings/Security Settings/Local Policies/Security Options. The policy is called: Network Security: Lan Manager authentication level.”
In our case there were also other NTLM policies that needed to be considered, so worth checking any of these:
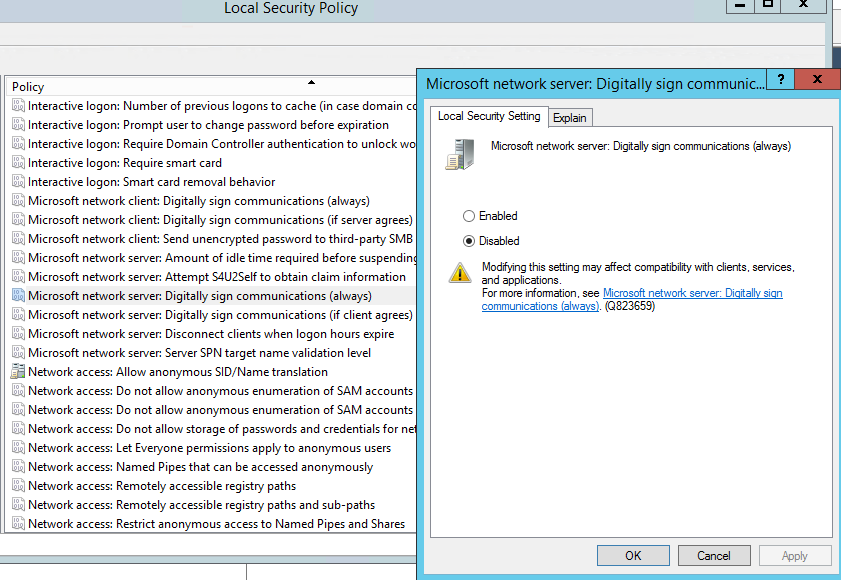
Also worth checking the policy: Microsoft network server: Digitally sign communications (always):
It is also possible to use different security settings within the /etc/fstab file on the vRO appliance, eventually we settled on sec=ntlmssp, however I believe the following are also possibilities: sec=ntlm, sec=ntlmv2, sec=ker5 and sec=ker5i
You may also want to consider using a credentials file rather than the username=xxx,password=xxxx in the /etc/fstab file if you want to get this past your security person ;-)