PowerShell 2.0: One Cmdlet at a Time 102 Disable-PSRemoting
Continuing the series looking at new cmdlets available in PowerShell 2.0. This time we look at the Disable-PSRemoting function. Note: This is a proxy command which calls the Disable-PSSessionConfiguration cmdlet.
What can I do with it?
Disable PowerShell remoting on a computer that has previously been enabled for remoting. Note: This command must be run from a PowerShell session with administrative privileges.
Example:
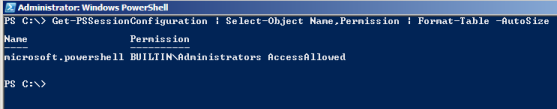
Retrieve the current PSSessionConfiguration settings. Disable PowerShell remoting, then retrieve the PSSessionConfiguration settings again to compare.
Get-PSSessionConfiguration Disable-PSRemoting Get-PSSessionConfiguration
Notice the PSSessionConfiguration on a machine enabled for PowerShell remoting
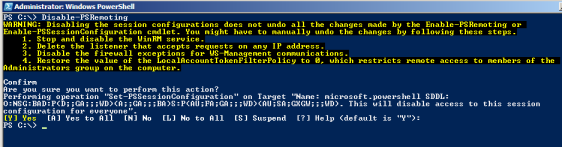
Disable PowerShell Remoting. You will receive the following warning that using this command does not necessarily reverse everythign that Enable-PSRemoting may have done.
WARNING: Disabling the session configurations does not undo all the changes made by the Enable-PSRemoting or Enable-PSSessionConfiguration cmdlet. You might have to manually undo the changes by following these steps. 1. Stop and disable the WinRM service. 2. Delete the listener that accepts requests on any IP address. 3. Disable the firewall exceptions for WS-Management communications. 4. Restore the value of the LocalAccountTokenFilterPolicy to 0, which restricts remote access to members of the Administrators group on the computer.
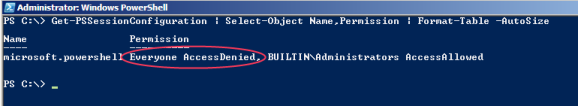
Now check the impact on the PSSessionconfiguration - the AccessDenied permission has been applied to Everyone.
How could I have done this in PowerShell 1.0?
Remoting did not exist in PowerShell 1.0, you would have needed to use Remote Desktop to run an interactive session on a remote server.